Phased Implementation of CMMC Requirements Has Begun!
CMMC Phase 1 Implementation (Nov 10, 2025 – Nov 9, 2026) to focus primarily on CMMC Level 1 and Level 2 self-assessments
Click HERE for details
The CMMC framework consists of the security requirements from NIST SP 800-171 Rev 2, Protecting Controlled Unclassified Information in Nonfederal Systems and Organizations, and a subset of the requirements from NIST SP 800-172, Enhanced Security Requirements for Protecting Controlled Unclassified Information: A Supplement to NIST Special Publication 800-171. The model framework organizes these practices into a set of domains, which map directly to the NIST SP 800-171 Rev 2 families. There are three levels within CMMC – Level 1, Level 2, and Level 3. Source
October 2025 – NDISAC Whitepaper: The Role of VDI for CMMC Now Available
CMMC Program Resources
DIB SCC Cyber / CMMC Training
The intent of the Defense Industrial Base (DIB) Sector Coordinating Council (SCC) Supply Chain Cyber training is to build awareness for DIB suppliers of the Cybersecurity Maturity Model Certification (CMMC) requirements and their obligation to meet FAR 52.204-21, basic cyber hygiene and specialized data handling and protection requirements aligned to DFARS 252.204-7012. For additional information, click here to access the DoD CIO CMMC 101 briefing.
The training below is self-paced and intended for a range of roles and responsibilities including, but not limited to, executives, project managers and technical staff from organizations seeking certification or assessment (OSC/A), and who need to comply with CMMC.
PowerPoint – Cyber/CMMC Training
Tip: Important information included in the notes section
When will CMMC be required on contracts?
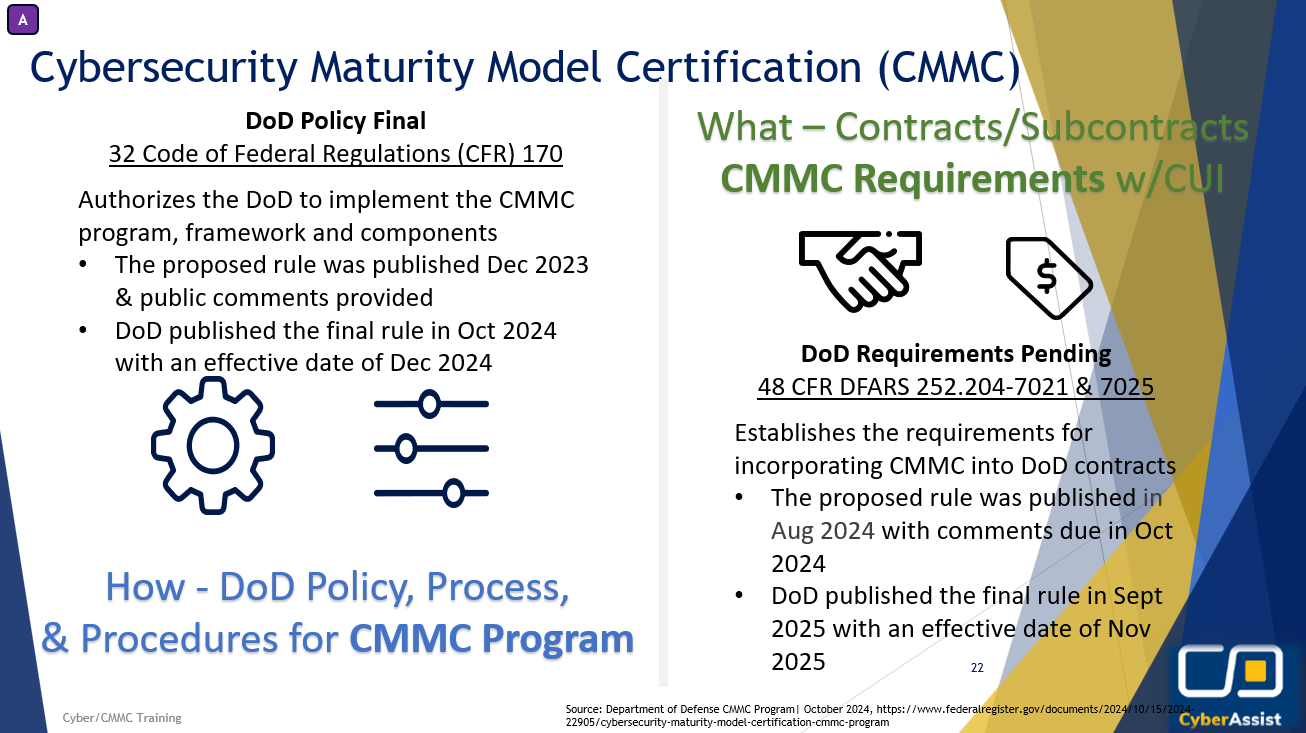
CMMC Program Final Rule – 32 Code of Federal Regulations (CFR) § 170
-
- The 32 CFR § 170 formally establishes the DoD’s CMMC Program
- It sets up the framework, components, policy, and procedures for how the CMMC Program will be implemented and managed
- The DoD published the CMMC Program Rule in October 2024
- The rule was effective as of December 2024
CMMC DFARS Acquisition Final Rule – 48 CFR § 204, 212, 217 and 252 (DFARS 252.204-7021 & 7025)
-
- Establishes the requirements for incorporating CMMC into DoD contracts
- DoD published the final rule in September 2025
- CMMC Phase 1 implementation of self-assessments became effective November 10, 2025
Source: Department of Defense CMMC Program | September 2025
CMMC Framework Overview
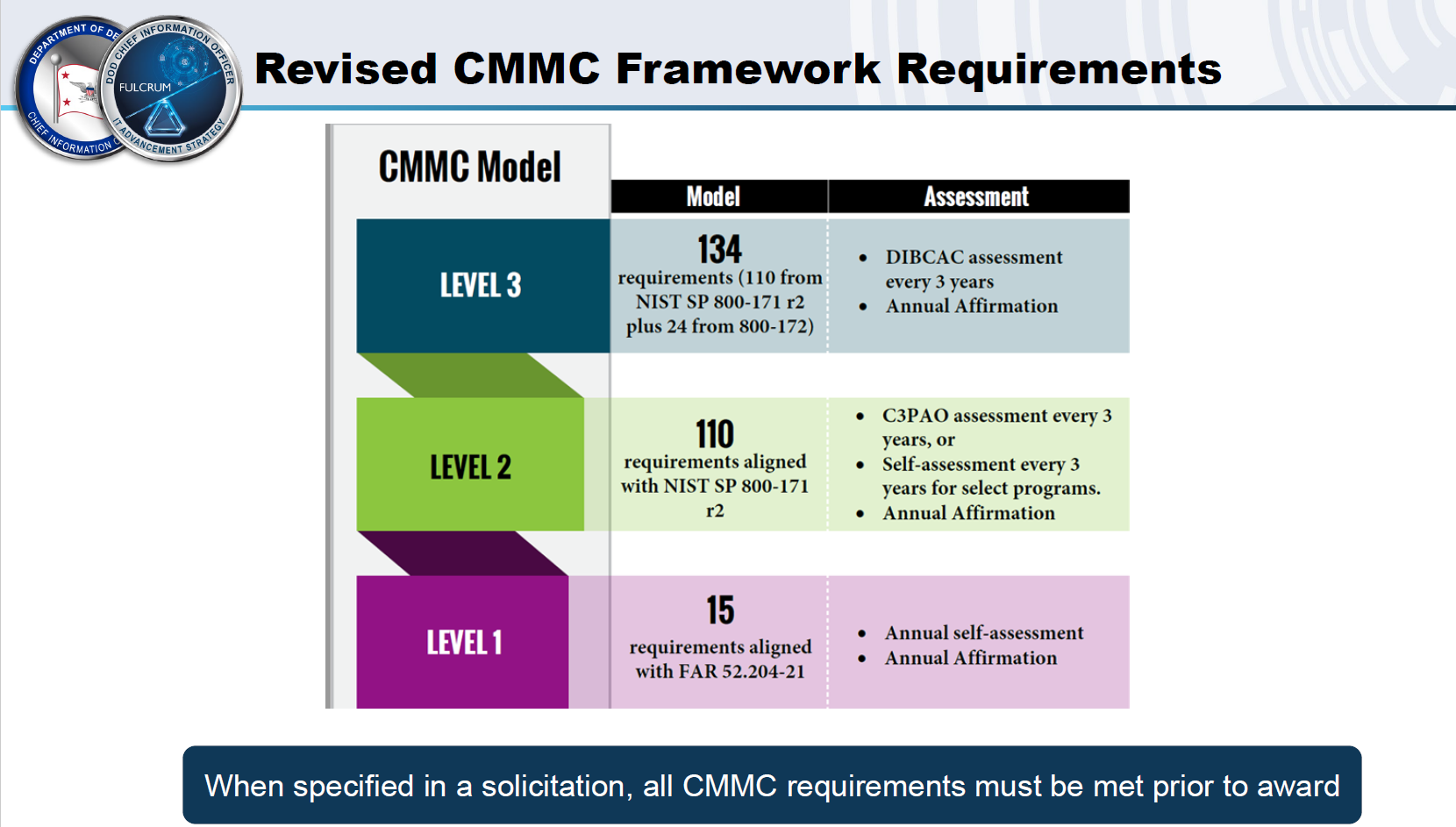
The CMMC model measures the implementation of cybersecurity requirements at three levels. Each level consists of a set of CMMC security requirements: as set fourth in 32 CFR § 170.14 (c).
-
- Level 1: Encompasses the basic safeguarding requirements for Federal Contract Information (FCI) specified in FAR Clause 52.204-21.
- Level 2: Encompasses the security requirements for Controlled Unclassified Information (CUI) specified in NIST SP 800-171 Rev 2 per DFARS Clause 252.204-7012.
- Level 3: Encompasses a subset of enhanced security requirements for CUI specified in NIST SP 800-172 with DoD-approved parameters where applicable.
Source: Cybersecurity Maturity Model Certification Model Overview Version 2.13 | September 2024
-
- CMMC is intended to be cost-effective and affordable for small businesses to implement at the lower CMMC levels.
- CMMC includes 14 domains (key sets of cybersecurity capabilities).
- All contractors and suppliers doing business with DoD must meet the CMMC Level 1 requirements at a minimum.
- The CMMC level of certification required for each DoD procurement will be specified in RFIs and RFPs
- Contractors will need to flow down appropriate CMMC Level requirements and verify supplier certification levels (CMMC Level 1 for FCI but no CUI; CMMC Level 2 or above for CUI).
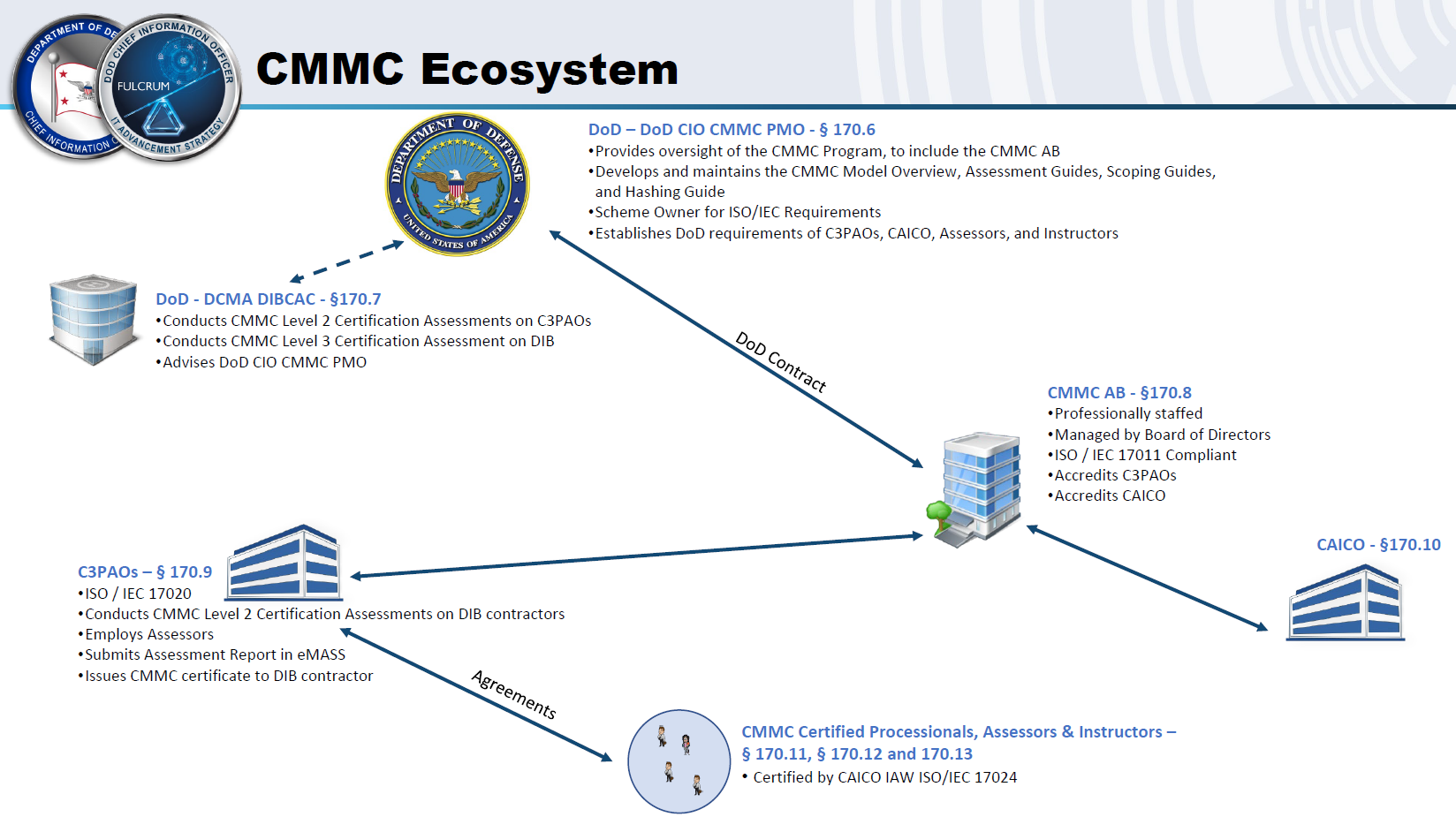
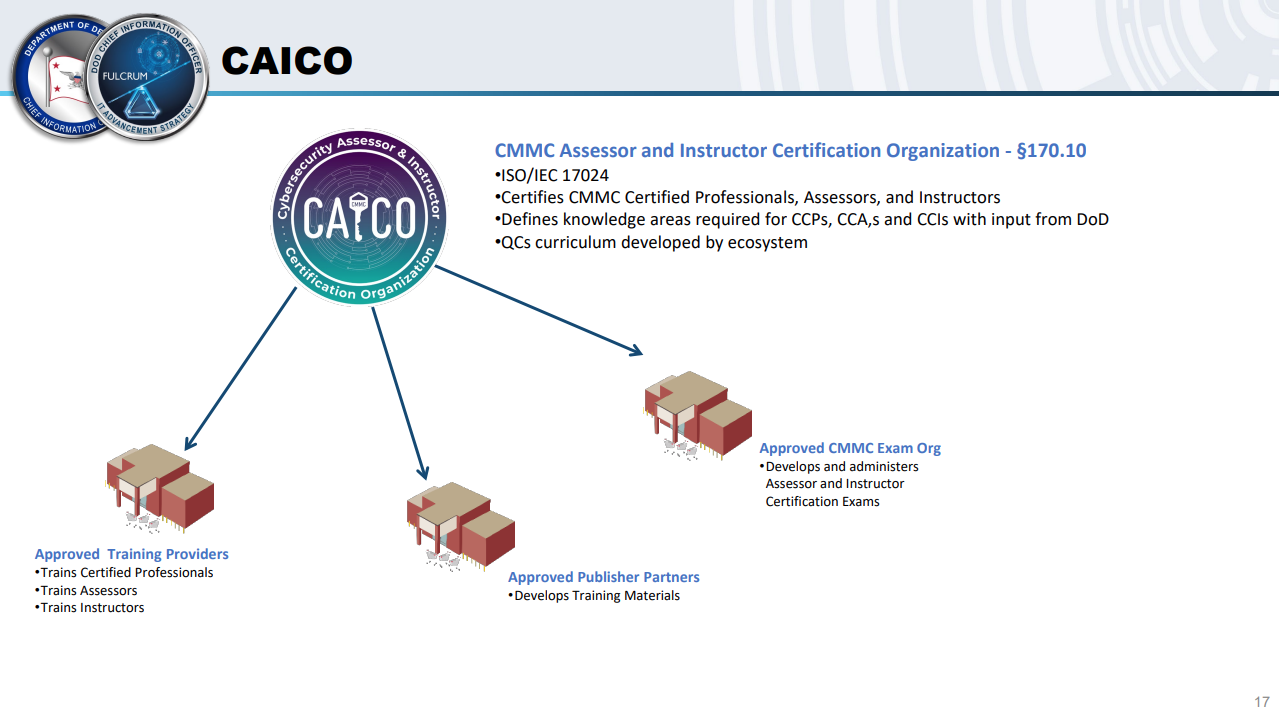
CMMC Ecosystem Overview
CMMC Security Requirements by Level
Select to see the security requirements and resources for each CMMC Level:
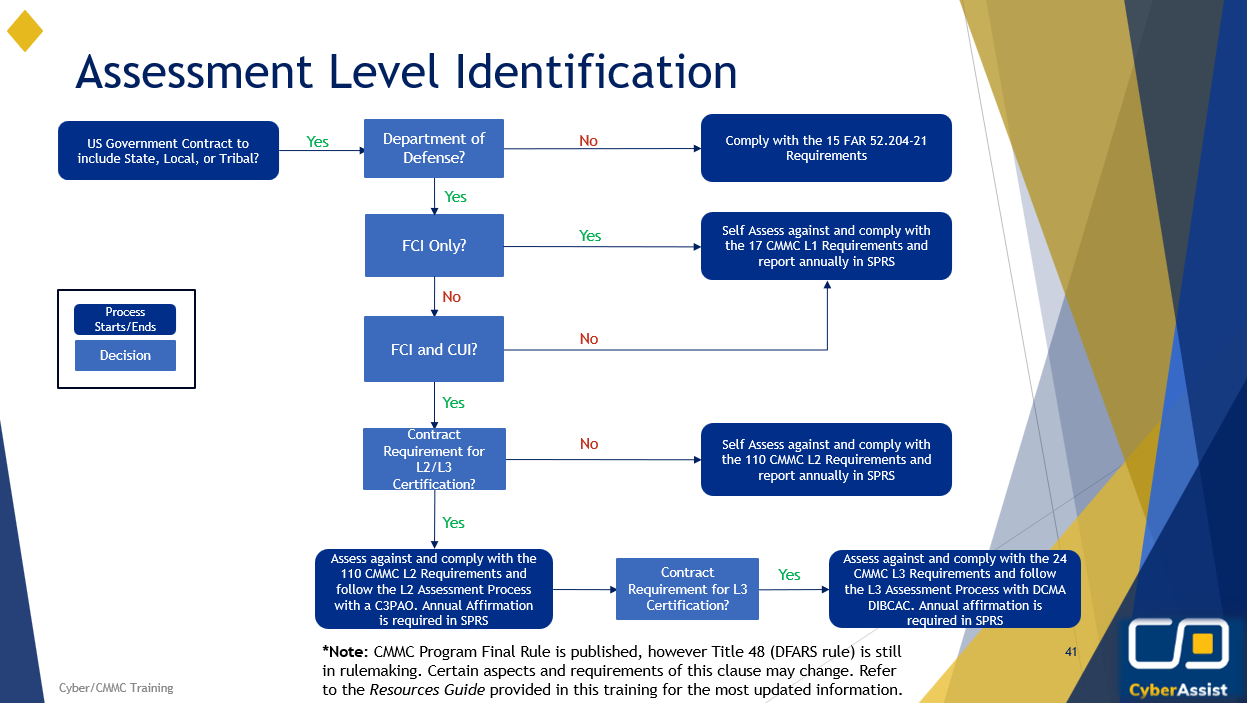
When CMMC “goes live,” organizations will need to determine the appropriate assessment path and level, given the type of information they have access to or develop
- Federal Contract Information (FCI) only
- Self-assessment of CMMC Level 1 (L1) requirements using the CMMC Self-Assessment Guide – Level 1 for additional guidance
- Controlled Unclassified Information (CUI) identified as Non-critical to national security *
- Self-assessment of CMMC L2 requirements using the CMMC L2 Assessment Guide
- CUI identified as Critical to national security *
- Requires certification by an authorized C3PAO from the Cyber AB Marketplace
- CUI identified as requiring enhanced protections *
- Requires CMMC L3 certification by DCMA DIBCAC* using the CMMC L3 Assessment Guide
In February 2025, the DoD released a memorandum with the subject: “Implementing the Cybersecurity Maturity Model Certification (CMMC) Program: Guidance for Determining Appropriate CMMC Compliance Assessment Levels and Process for Waiving CMMC Assessment requirements” that further define how Program Managers and requiring activities will identify the appropriate level for a given contract.
CMMC Security Requirements by Domain
The CMMC model consists of 14 domains that align with the families specified in NIST SP 800-171 rev 2.
