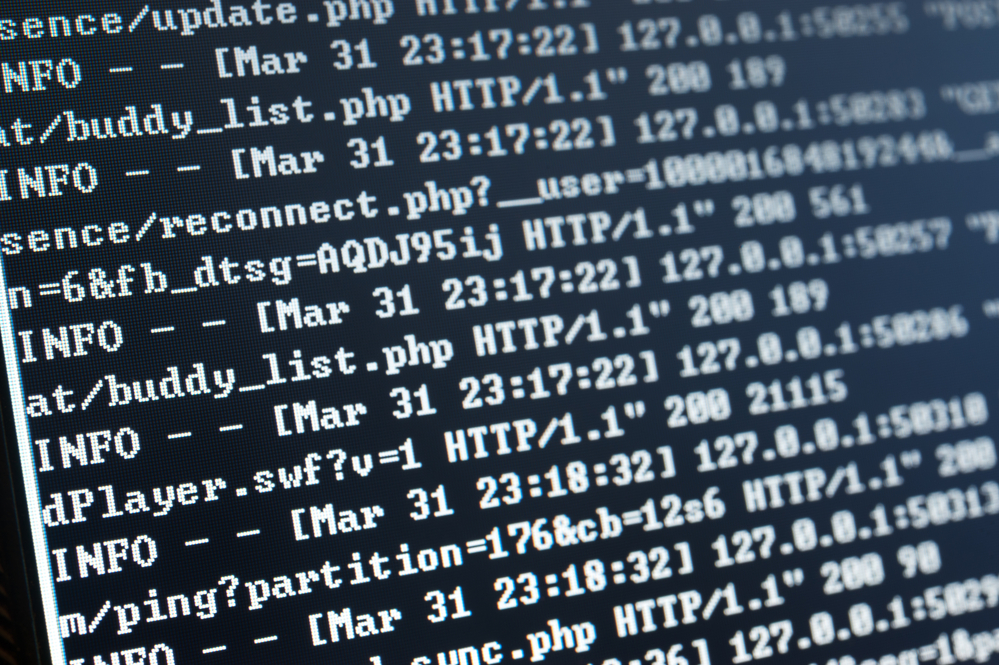
Log management is key to ensuring that computer logs and records are maintained in sufficient detail for an the appropriate period of time needed by an organization.
This article lists Security Information and Event Management (SIEM) tools that provide log analysis and correlation of events. Caveat: Open source may be sufficient for some small companies but do not provide support and may offer only a limited feature set. Most of these open source solutions offer a paid option as well. If you try it and like it, upgrading to the paid option to gain support and features is easy. This link provides a list of no or low cost log management tools. A listing of SIEM tools provided by Gartner. This document from Ubuntu discusses Logwatch, a tool that will monitor your server's logs and email the administrator a digest on a daily basis. This article describes the concept of Unified Threat Management and how implementing UTM will aid in identifying unauthorized access and use. Best practices for Windows Auditing Log monitoring and different types of windows audit logs This is an example of a logging policy, including system and application logging elements that if logged correctly, will aid in identifying unauthorized access and use. This guideline describes the risk of inadequate logging, defines events to be logged and establishes a case for using an automated tool for log review.
This document provides assessment guidance for Level 1 of the Cybersecurity Maturity Model Certification (CMMC). This document provides assessment guidance for conducting Cybersecurity Maturity Model Certification (CMMC) assessments for Level 2. The purpose of this publication is to provide procedures for assessing the CUI requirements in NIST Special Publication 800-171. This policy provides an example of events surrounding confidential or restricted information that are typically logged. While this example is for health information, the log requirements would apply to other restricted information as well. The policy includes a description of log reviews.